DOE Calls for New Cybersecurity Tech Amid Energy Infrastructure Threats
Applications are open for the second cohort of the Clean Energy Cybersecurity Accelerator, a program from the Department of Energy and National Renewable Energy Laboratory aiming to tackle the latest threats targeting the power grid.
Amid increasing attacks on energy infrastructure, the U.S. Department of Energy (DOE) and National Renewable Energy Laboratory (NREL) seek fresh ideas to beef up the nation’s resilience to physical and virtual threats.

Composite image of virus background. Image used courtesy of Adobe Stock
Up to five U.S.-based participants will be selected for the second cohort of the Clean Energy Cybersecurity Accelerator, which targets technologies aiming to solve hidden risks due to incomplete system visibility and device security/configuration. The deadline to apply is Feb. 10.
The program extends for three to 12 months. To assess their solutions, participants will have access to the NREL’s Advanced Research on Integrated Energy Systems cyber range, which connects to more than 20 megawatts of energy system hardware and allows users to run tests through realistic scenarios. Three major utilities—Berkshire Hathaway Energy, Duke Energy, and Xcel Energy—have teamed up with the program to use the technologies once they’re validated.
Increased Demand for Energy Security Systems
The announcement comes as the nation’s power grid faces increasing digital and physical threats, reaching their highest level in 2022 with 101 attacks on electricity equipment reported through late August, according to reporting from Politico.
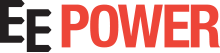
Perhaps the most visible event of the year happened in December when two Duke Energy substations were hit by shootings in Moore County, North Carolina, creating a massive outage spanning five days and affecting 45,000 customers.
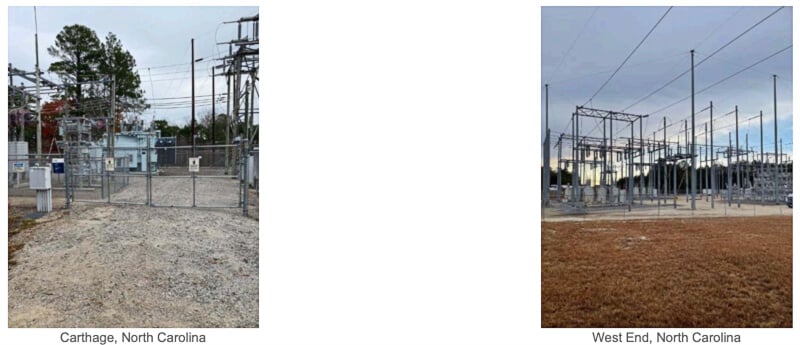
In December 2022, two substations spread 10 miles apart in Moore County, North Carolina, were targeted in a shooting that left 45,000 customers without power. Image used courtesy of the Federal Bureau of Investigation
In another story out of the Pacific Northwest, at least six physical attacks on electric substations in Oregon and Western Washington between November and December remain unsolved, per reporting from Oregon Public Broadcasting.
Last year, several other physical attacks targeted energy systems in Florida, South Carolina, South Dakota, Oklahoma, California, and other states. According to the U.S. Government Accountability Office, nations and criminal groups represent the most significant cyber threats to critical domestic infrastructure.

The U.S. Department of Energy chart shows how distributed energy resources connect to the grid through a cybersecurity foundation. Image used courtesy of DOE
Ongoing cybersecurity issues were the subject of a 29-page report released by the DOE in October 2022, in which the agency outlined potential attack vectors targeting distributed energy resources (DER), such as ransomware, supply chain compromise attacks, botnets, and worms. It mentioned various challenges in addressing cyber threats, such as gaps in standardized procedures, the need for a DER trust model, and the importance of balancing critical functions while mitigating attacks.
The DOE also said that many existing standards and best practices would need to be updated to fit DER deployment use cases across multi-factor authentication, endpoint detection and response, encryption, and other areas.
DOE, NREL Head Cybersecurity Accelerator: Three Selected for First Cohort
The inaugural Clean Energy Cybersecurity Accelerator cohort recently began its technical assessment phase in December, focusing on authentication technologies to be applied across distributed energy resources.

This map shows all electric power transmission lines in the mainland United States. Image used courtesy of the Energy Information Administration via the U.S. Energy Atlas
Three participants were selected for the first cohort: Virginia-based cybersecurity startup Blue Ridge Networks (with a system to secure IT network operations from external discovery or data exfiltration), aerospace and national security contractor Sierra Nevada Corporation (offering software integration to boost safety in unauthenticated ecosystems) and California-based zero-trust security firm Xage (with identity-based access control).
Video used courtesy of YouTube
For its second cohort, the program targets technologies that identify all industrial control system assets linked to a utility’s infrastructure and provide methods to remove unauthorized or compromised assets.