Defending the Smart Grid Against Inverter Attacks
Researchers highlight smart inverters' vulnerabilities to several cyberattacks and possible defenses against them.
Electrical power grids are transforming into smart grids with the emergence of distributed energy resources (DERs). Remote control functions, data acquisition, and automation in these systems aim to improve the efficiency of power systems and change how power gets distributed.
Transmission lines, part of the electrical power grid. Image used courtesy of Adobe Stock
DERs are small-scale supply and demand management resources interconnecting to the electrical grid. They manage the power systems the same way large central power plants work. Conventional power stations are centralized and require electricity to be transmitted over long distances. On the other hand, DERs are decentralized, modular and located on the consumer side. It comprises many power generation and storage components, such as inverters and batteries.
One of the major issues with intermittent power sources like wind or solar power is that the supply-demand relationship becomes very complex. DERs solve this problem using optimization algorithms and tools to balance the network. In a nutshell, DERs ensure, at all times, that demand matches electricity generation. Therefore, reducing electricity needs has the same effect as increasing power generation.
DERs can store excess power in batteries and return power to energy grids, making them an attractive tool for decentralized energy management. Advances in this technology could lead to scenarios where electricity generation is localized, and consumers become less dependent on the grid.
Interconnectivity and Vulnerability
With these promises, DERs are becoming more prevalent now. But with interconnectivity comes a variety of vulnerabilities from cyberattacks. DERs rely on smart inverters for connectivity with power grids. With the rise of installed solar capacity, traditional inverters are being upgraded to smart inverters with two-way communication.
Interconnectivity comes with a variety of vulnerabilities from cyberattacks. Image used courtesy of Adobe Stock
In smart inverters, voltage sensing and related mechanisms maintain the voltage level within an acceptable range. The attackers might target these control systems and cause a collapse of the distributed systems. Moreover, false data injection (FDI) can lead to a major power outage event in a power system. Therefore, attack and defense or smart inverters is a new field of study representing growing concerns of this emerging technology.
Researchers at Concordia University show, in their paper published in IEEE Transactions on Power Electronics, how smart inverters can get attacked by malicious sources and how serious these attacks get for the public. Moreover, they look for ways to defend against those attacks and how to prevent them.
Potential Threats at Consumer and Grid Levels
Study coauthor Jun Yan, associate professor at the Concordia Institute for Information Systems Engineering, comments that threats are inevitable as there are so many homeowners and third-party services using smart power systems. He further adds that a perfect line of defense is almost impossible.
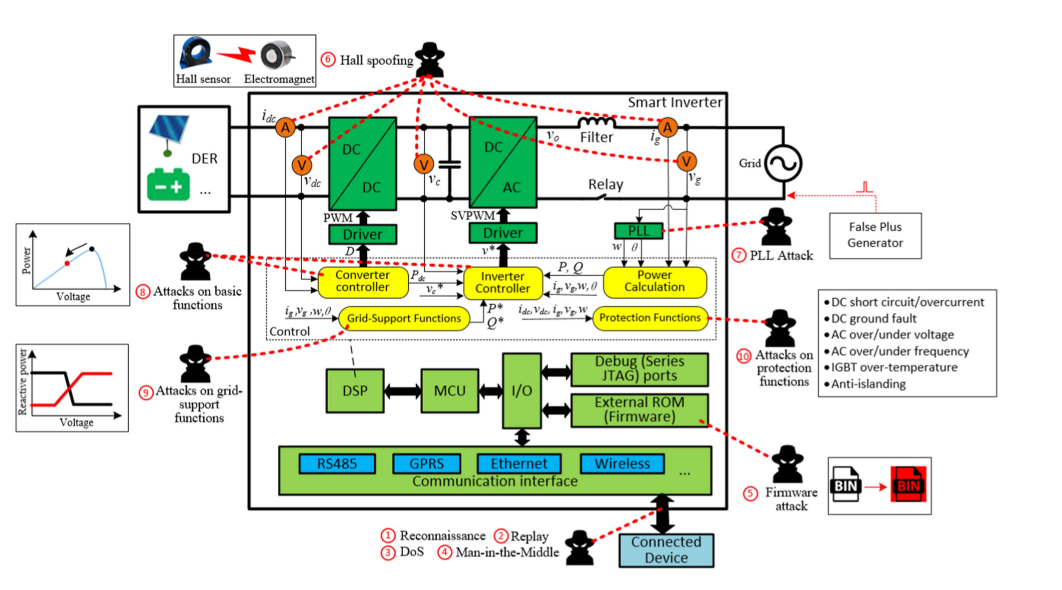
A smart inverter in a DER system consists of a DC-DC converter, an AC-DC inverter, PWM (Pulse Width Modulation) controllers, voltage and current sensors, phase-locked loops (PLLs), low-voltage microcontrollers, digital signal processors (DSPs), external read-only memory (ROM), communication interface, control and protection functions. The DSPs provide PWM signals to control power converters, which can be manipulated with external fields or signal injection.
The researchers, based on the device architecture, describe multiple forms of attacks on smart inverters and threats to the entire electrical grid. Cyberattacks on inverters can hamper communication between the grid, the energy regulators, and other devices. They report that hardware attacks are also possible.
Possible attacks on smart inverters. Image used courtesy of Concordia University
The team identified DDoS and Man-in-the-Middle as possible attack strategies on the communication links. Hardware can be threatened by external fields around the device, which can lead to oscillations or corruption of power, voltage, and frequency, impeding the DER's attacks to distribute energy. Moreover, they identify attacks designed to inject false data into the communication links between the DSP and the power regulator.
The researchers believe their review will help industries review their line of defense and improve their security. They further aim to use deep learning to find effective ways to attack smart grids and identify more potential impacts.