New Database Aggregates ‘Software Bill of Materials’ for Utility Cybersecurity
Aiming to combat cybersecurity threats that could take down the grid, a new database aggregates software vulnerabilities, component risks, exploitability, and other critical security information for utility vendors and suppliers.
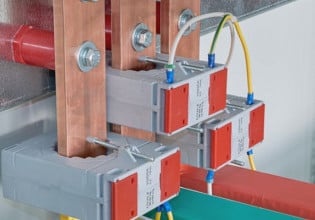
At Distributech International in California this week, Florida-based Fortress Information Security unveiled a new database that offers a software bill of materials (SBOM) repository for every vendor in the utility industry.
The North America Energy Software Assurance Database (NAESAD) aims to help utility companies identify and remediate vulnerabilities in any software that manages critical energy applications. It compiles a comprehensive set of SBOMs, documents that detail a given application’s software components, proprietary and third-party integrations, and other aspects of the code.
The NAESAD platform launches in partnership with investor-owned utilities such as Ohio-headquartered American Electric Power, which serves 5.5 million customers in 11 states, and Avangrid Networks, a Connecticut-based firm with 3.3 million customers across the northeast.

At Distributech International in San Diego, Fortress Information Security unveiled its new SBOM database for the energy industry. Image used courtesy of Fortress via Twitter
Fortress says on its website that its security solutions serve 40% of the domestic power grid and help to secure over 1 million assets. In addition to energy and utility companies, Fortress also sells to government agencies and critical manufacturers.
Third-party risk assessment services are nothing new in the industry, but NAESAD builds on Fortress’ existing A2V Network library, which provides access to security assessments for more than 50,000 vendors.
Video used courtesy of YouTube/Fortress
Growing Interest in ‘Software Bill of Materials’ Frameworks
SBOMs are of growing interest in government contracting as regulators are exploring or introducing new requirements for companies that do business with infrastructure-presiding agencies and other federal departments. In May 2021, President Joe Biden signed an executive order directing federal agencies to build a framework to require SBOMs for the software packages they use. The Federal Times recently reported that some SBOM policies are now being mandated, with more on the way.

A visualization of how a software bill of materials (SBOM) works. Image used courtesy of the National Telecommunications and Information Administration
Fortress’ SBOM database comes amid growing concerns about data breaches, malware/ransomware, and other cybersecurity threats emerging with the potential to bring down the power grid.
Cyberattacks are increasing across the board, but few have risen to the scale of potentially bringing down critical infrastructure. One high-profile example is the 2020 supply chain attack that hit SolarWinds, a company providing software to thousands of public and private customers, including energy firms. Another is the Log4j remote code execution vulnerability, which impacts an Apache open-source logging framework that’s incorporated into thousands of products spread worldwide. Last year, the U.S. Cybersecurity and Infrastructure Security Agency listed Log4j as one of the top vulnerabilities routinely exploited by hackers in 2021.
Attacks aiming to disrupt entire supply chains are growing in frequency and scope. The European Union’s Agency for Cybersecurity (ENISA) reported in 2021 that 66% of such attacks start with exploiting vulnerabilities in the supplier’s code. ENISA’s recent 2022 Threat Landscape Report further profiles the ongoing rise of supply chain compromises, which accounted for 17% of intrusions in 2021 compared to less than 1% in the previous year.
Software supply chain attacks often stem from open-source development libraries, software packages, and known compromises. Underscoring the need for an SBOM framework in supplier relationships, ENISA’s recent report cited a PWC survey in which only 40% of respondents said they understood their third party’s cyber/privacy risks. Another survey by BlueVoyant found that 38% of respondents are largely unaware when issues arise with a third-party supplier’s security.